Real estate refers to property in the form of land, buildings, and natural resources. It is a significant and diverse industry that encompasses various aspects of property ownership, development, management, and transactions.
Here are some key points about real estate:
*Types of Real Estate: Real estate can be categorized into various types, including residential (homes and apartments), commercial (offices, retail spaces, and industrial properties), and agricultural (farms and ranches). Additionally, there is specialized real estate like hospitality (hotels and resorts), healthcare (hospitals and clinics), and more.
*Property Transactions: Real estate transactions involve buying, selling, leasing, or renting properties. These transactions are typically facilitated by real estate agents or brokers who help individuals and businesses find suitable properties or buyers.
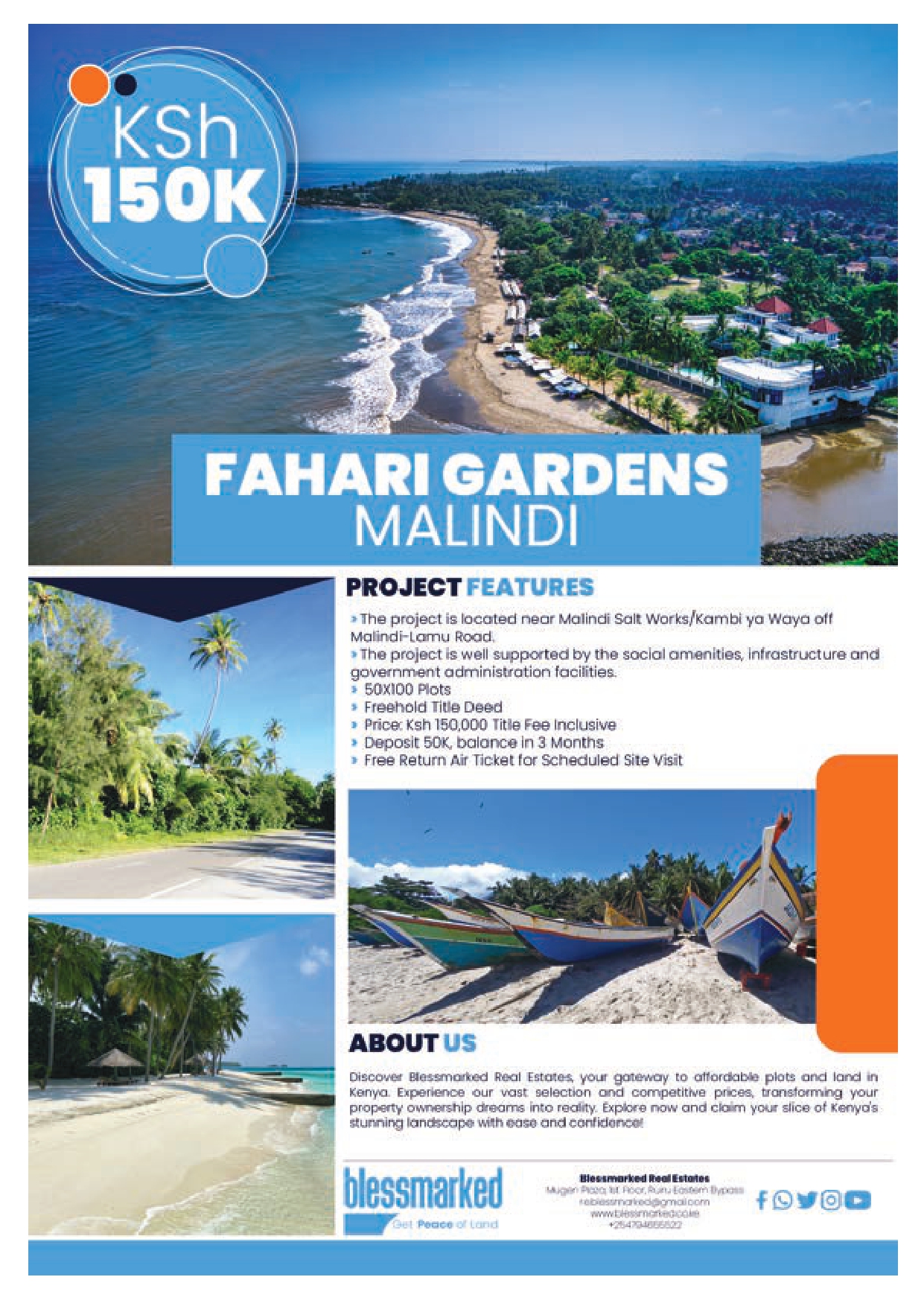
*Real Estate Development: This involves the construction and improvement of properties. Real estate developers purchase land or existing properties and develop them for various purposes, such as residential communities, shopping centers, or office buildings.
*Investment: Many people invest in real estate for the potential for income and capital appreciation. Real estate investments can include owning rental properties, investing in real estate investment trusts (REITs), or purchasing property for long-term growth.
*Real Estate Financing: Buying property often involves obtaining a mortgage or financing. Financial institutions provide loans to individuals and businesses to facilitate property purchases.
*Real Estate Regulations: Real estate is subject to various regulations and laws, including zoning regulations, building codes, property tax laws, and landlord-tenant laws. Compliance with these regulations is essential for property owners and developers.
*Market Trends: Real estate markets can fluctuate, with factors like economic conditions, interest rates, and local demand affecting property values and rental rates.
Real Estate Professionals: The real estate industry employs various professionals, including real estate agents, brokers, appraisers, property managers, architects, and contractors.
Real estate is a significant asset class and plays a crucial role in people's lives, whether as a place to live, work, or invest. It can be a complex and dynamic field, and its dynamics can vary significantly depending on location and property type.
Read The Publication